Security assesment of commercial Alarm Systems
The article aims to analyse the security of alarm systems. It explain how alarm systems work and what are the ways of defeating an alarm.
- How alarm functions? The alarm detect the breach, then call or message the security company.
- How to attack an alarm? The attacker may try to block the detection or may try to block the transmission of the message to the security company.
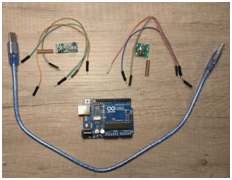
The article explains in instructables below (Read HowTo) through detailed movies ways to defeat an alarm and how to bypass a magnetic door sensor. It provides the experiments done: components used in the experiment, indications to wire-up the test-system, provided code to be uploaded in order to complete the system-test with attacking (for instance: cloning) functions.
The following weaknesses were identified:
- GSM and Wireless Jamming – commercial devices that are legal to be bought by anyone


How to prevent: (1) use an alarm that supports an ethernet cable and sends email or other alerts via the internet; (2) install the alarm central unit in the middle of the house, so that the jamming device is less effective due to distance.
2. Cloning Wireless Signals – simple experiment that reveals that using cheap components and following simple routines of wiring-up cables, signals may be cloned
How to prevent: (1) buy an alarm system that offer encryption and rolling codes for the remote control and sensors; (2) search for alarm systems that have an alternative arm by SMS or voice call.
3. Fooling Door / Window Sensors – the device dependency of the magnetic field, as part of the sensor mechanism, may lead to finding ways to keep the switch “ON”
How to prevent: (1) install the switch on a metal surface, the metal will absorb most of the magnetic field; (2) hide the sensor so attackers can not identify it’s location.

4. Other Methods
- Movement sensors hack: some sensors may be fooled by reducing radiation footprint (by wearing heat protective clothing or by moving slowly)
How to prevent: buy alarms with Doppler radar motion sensors, its are not fooled by heat or slow movement.
- Cloning and replaying random sensor signals: trigger false alarms by replaying random sensor signals
How to prevent: buy alarm system that uses encryption and rolling codes; buy sensors with wires
- Misconfiguration: such as configurable “delay” attribute will allow the attacker to locate the alarm and switch it off.
How to prevent: try to wisely make use of all configurable alarm attributes.
- Loosing the element of surprise: be mean, pretend you haven’t read this article and don’t know anything about alarms; let the attacker believe you are exposed!
How to prevent: do not install the sensors too obvious in the house
We strongly believe that article helps both the final consumer so he/she may prevent themselves from unplanned security breaches, and that also the business to improve thei devices and their functions to overcome their weaknesses.
Article date: Feb 18, 2017
Read HowTo
https://www.instructables.com/id/Alarm-System-Security-Put-to-the-Test/
